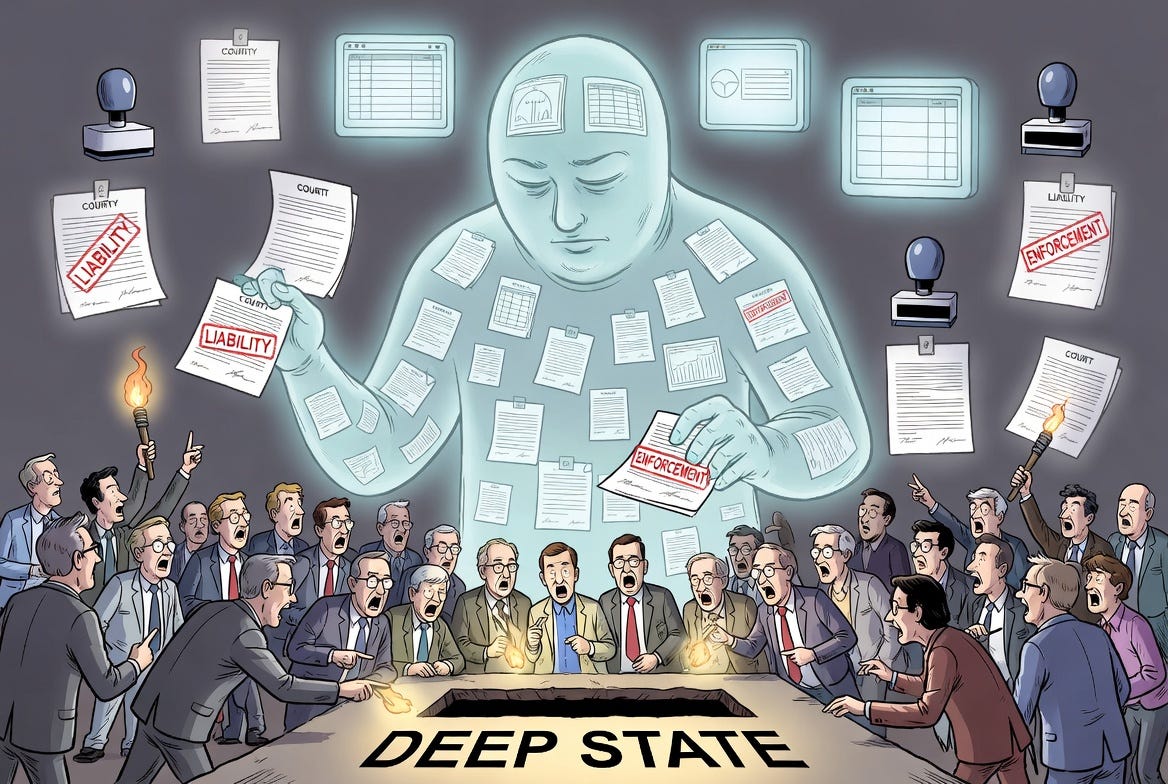
The "Deep State" vs the "Ghost State"
One claims power is secretly taken. The other shows authority no longer needs to be.
In working on so-called “ghost courts” — synthetic tribunal identities that do not map cleanly to law — I have been quietly collaborating behind the scenes with others exploring the simulation of authority. They are probing many parts of the UK state via Freedom of Information Act (FOIA) requests — councils, tax collectors, regulators — and a clear picture is beginning to emerge from the responses.
While much attention is heaped on an alleged “Deep State”, where power is said to be usurped by infiltration, a parallel and arguably more immediate phenomenon is becoming visible. This is the “Ghost State”, where bureaucracy makes binding demands, but cannot readily produce a coherent evidential record showing how that authority lawfully attaches.
The purpose of this article is not to provide a detailed comparison of the two phenomena, nor to attempt a complete account of the “Ghost State”. Rather, my ambition is limited to setting out the key characteristics of an emerging “ghost layer” of government:
lawful form is preserved on paper in principle, but operational authority in practice is exercised through opaque systems, records, and processes — that cannot be cleanly traced back to that lawful form.
The effect is that the public face enforcement — of debts, fines, taxes, obligations — in circumstances where the legitimate exercise of law cannot easily be distinguished from the illegitimate. Only extraordinary effort and significant personal cost, of the kind I have undertaken, begin to make it possible to peer through that fog.
Before I present the patterns that define the “Ghost State”, there must come a prelude. The critical distinction is that the “Deep State” is necessarily conspiratorial — hence the language of “conspiracy theories” — whereas the “Ghost State” admits of a far more prosaic explanation.
The latter does not require hidden actors or coordinated intent. It can arise from entirely visible forces: scale, cost pressure, digitisation, outsourcing, and the fragmentation of responsibility across institutions and systems. In that sense, it is structurally produced rather than secretly imposed.
That does not make it benign. On the contrary, the resulting opacity is, at the very least, awfully convenient. A system in which authority becomes difficult to trace is one in which accountability becomes equally difficult to enforce. You cannot easily contest decisions where the act or actor become indeterminate on the record.
The “Ghost State” Patterns
Distilling out our collective interaction with the state (via AI) reveals a set of patterns that recur. Again, this is not definitive research, but a tentative interim presentation to share the concept and solicit feedback.
1. Statutory term → operational alias
My own question began where the statutory court was substituted with an administrative label — “North and West Cumbria Magistrates’ Court (1752)”. This is not an isolated example. Councils, for instance, are required by law to issue a “demand notice”, but often label it a “bill” — which carries a different meaning in law, implying a contractual demand for services rendered, subject to specific constraints.
This switch is not cosmetic. It severs the link between:
the statutory trigger, and
the document the citizen actually receives.
The substitution alters how the demand is understood and responded to: the citizen engages with the operational form, not the legal mechanism said to underpin it. If it looks like a bill, and is presented as a bill, then the natural response is to assess it as such — while in reality it is treated under law as something else entirely.
The effect is that liability is enforced without the statutory language that defines it.
2. Hidden ignition point
To this day I have been unable to determine which court was seised of my motoring matter, or precisely when. That moment is the “ignition point” of authority.
Every lawful coercion requires such a point of attachment:
Who initiated the case?
What document created liability?
When did it occur?
Across all domains, the effect is visible, but the trigger is obscured. The originating act — the point at which legal authority is said to attach — is distributed, automated, or embedded within opaque processes.
You can see enforcement, but not the lawful act that justifies it.
3. Records become the authority
In my motoring case, there has never been a definitive mapping between the entries in the operational documents (e.g. notice of fine, register extract) and the triggers for jurisdiction. Rather, the system behaves as if:
“If it’s in the computer system, then it’s real.”
But when challenged, there is:
no clean originating act,
no identifiable decision-maker,
no verifiable chain.
Administrative text begins to do the work that law has not fully performed. The record ceases to function as evidence of authority and instead operates as a proxy for it.
4. Fragmented responsibility
When you attempt to reconstruct the evidential chain of authority, you hit a wall. Whether through GDPR Subject Access Requests or FOIA requests, the outcome is the same, over and over:
“Not held here”
“Too burdensome”
“Operational matter”
“Case-by-case”
“Held by contractor”
“Retention expired”
Operational responsibility is distributed so widely across institutions, systems and contractors that no single actor can cleanly reconstruct the full legal chain.
The result is that accountability dissipates across the joins.
5. “Operational necessity” replaces legality
The more automated the system is, the greater its tendency to rely on abstraction rather than the explicit exhibition of the record by which decisions are made. The very volume of the system makes challenge sensitive, lest a defect propagate at scale.
This creates a somewhat perverse and paradoxical incentive with its own circular logic:
“We need to process at great scale, therefore we adapt the system for lower scrutiny.”
But:
that adaptation is not fully legislated,
not transparently defined,
not legally auditable end-to-end.
Systems designed for scale and efficiency place pressure on traditional safeguards, with workflow increasingly determining outcomes that the statutory framework is assumed — but not always able — to support.
The outcome is that workflow quietly replaces law as the governing mechanism.
6. Limb collapse (Act / Scheme / Hybrid)
This is where some legal subtlety enters. There are three fundamental modes of authority:
Act — a specific, concrete lawful act (e.g. a validly issued notice)
Scheme — the statutory framework operating through general rules and conditions, without requiring a single focal act to be identified by the citizen
Hybrid — for example, ignition by a specific act, followed by administrative continuity from that point on
The problem is the third, when it becomes unverifiable:
the system looks like (1) + (2),
but actually operates as (2) + (black box)
The statutory scheme remains. The act disappears into workflow — and with it, the ability to clearly contest it.
7. Loss of verifiability
When distinct legal acts are no longer required, this creates a challenge for verifying that authority was properly instantiated in the individual case. That traditional rule of law requires the citizen to be able to ask:
Who acted?
Under what authority?
When?
By what instrument?
Where is it recorded?
But in this “ghost state” diffused model, those questions cannot be answered cleanly by any single authority without disproportionate effort.
That is the constitutional fracture — because it opens a space in which authority can be mimicked without easy detection.
8. FOIA as X-ray, not tool
Detecting the “Ghost State” is not straightforward, as it requires constructing the absence of proof of authority. The silences are therefore every bit as diagnostic as the answers. In particular, the pattern of non-answers becomes the “tell”. I have personally experienced this through my own FOI requests into the court labels being used.
Across responses you see:
fragmentation of identities (my 44 court names),
procedural shielding (“look here, not here”),
absence of canonical records (and therefore no referential integrity), and
reliance on interpretation rather than rule.
The bureaucratic system cannot clearly describe its own operation in legally coherent terms.
The opacity is not incidental; it is structural and load-bearing.
9. Public/private blur
When we are confronted with an entity like a court, a bank, or a debt collector, we see a singular identity. In reality, there is a complex network of actors, both internal and external, operating behind it.
Between statute and citizen now sit:
software systems
outsourced processing
enforcement contractors
automated notice generation
Yet legal accountability still assumes:
identifiable public officials exercising traceable authority
That assumption no longer reliably holds in practice — so accountability declines as responsibility diffuses.
10. Not error — system design
When confronted with an illegible and unintelligible system, the natural reaction of the citizen is to assume it is operating in error. We default to expecting coherence and precision, especially in claims to authority. But that assumption is misplaced.
This opacity and lack of grounding is not incompetence, or an isolated procedural failure. Rather, it reflects a scalable governance model, driven by volume, cost and risk distribution.
Verifiability is not a primary design constraint. The result is a system that preserves legal appearance while distributing operational power across processes that are difficult to audit end-to-end.
Taken together, these characteristics do not abolish the legal framework. The statutes remain, the language persists, and the formal structure appears intact. What changes is something subtle but consequential:
the ability of the citizen to test whether that framework has been lawfully applied in any given case.
Authority is no longer reliably anchored to
a clearly identifiable act,
performed by a recognisable decision-maker, and
recorded in a form that can be independently verified.
Instead, it emerges from a chain of systems, processes and records that produce outcomes without a correspondingly clear account of their legal origin.
What remains is not the absence of law, but the weakening of its traceability.
The bottom line is this:
The state no longer needs to openly break the law.
It only needs to make the source of its authority difficult to locate, identify, and verify.
When the state cannot show, in a clear and human-verifiable chain, how its authority attached to a citizen, what is being exercised is not the rule of law — but a simulation of it.
That is the “Ghost State” — and it is far easier to demonstrate than the “Deep State”.


Thank you, Martin. You are an undeniable seeker of truth, gifted with an insightful knack for exposing it in simple segments. I’m in California .. where somedays the battles for truth are cloaked at such cavernous depths it actually feels like navigating a snake pit. But my question is: How can you continue to impart your genius analysis without ever an utterance of the EFF BOMB? I’m a nice lady, but can’t seem to consistently display any decorum to actually demonstrate it. I need to read you more often, because you are truly GOD’s GIFT TO DECENCY in this, excuse me for saying it: THIS EFF’ed UP WORLD. MAGA strong here. Be well & thank you.
Martin, you've clearly pegged one aspect of this system in this article, which is the impact of ghost operations outward against the citizen. In past articles you have discussed how institutions fail over into continuity under stress. It appears to me that that aspect is the inner equivalent of this outer aspect.
Further, when you take this system and harness the desire for continuity in its internal operations, what you get is a corrupting influence on the people who operate the system.
Even if one of these people is otherwise a God-fearing person, he must still bow, consciously at first and increasingly unconsciously as time goes on, to the operation of the system as a matter of necessity, of continuity. It wears even the good people inside the system down until they become things, robots, cogs who can no longer see or respect the humans that they are demeaning in their everyday work. As the internal people become more and more likely to dehumanize the citizen they affect, they themselves become less human, more able to be controlled by the system and those who run it.
Additionally, the small number of psychopaths in the internal working population begin to thrive like successful parasites, eventually running the system because of their inborn drive to power and sadism.
When the legal system becomes divorced from the Law and the guardrails of proper action, the corruption evolves while the workers devolve.
Eventually, the people on all sides become ... nothing.
There is only ... The Machine.